Created by
Cristina L. Suing
TOPIC: WiFi: How Safe is that “Free” Public WiFi?
GRADE LEVELS: 6-8 Grade
LESSON DURATION: 90 MINUTES
SOFT SKILLS: Communication, Collaboration, Problem Solving
Learning Outcome: Students will present the basic safety issues of public WiFi.
- Students will determine the safety of different WiFi settings through a small group exercise.
Objective:
Given the reading materials, guided questions, video web and graphic organizer, 75% of the middle school students will be able to:
- Identify the definition of WiFi security and how it impacts their valuable information
- Analyze the security issues involving the WiFi security and its impact to the people
- Create a campaign poster for people awareness of the danger of using public WiFi with 100% success.
Standards of Learning:
SOL 6.8 Planets and the solar system
SOL P.S. 11 Electricity
Materials:
Explanation sheet with basic information
- Scenarios for group work/analysis
- FTC OnGuard Online: Video for review of information (Public WiFi networks)
Computer lab.
Art materials : colored pencils, markers, crayons
Activities:
- Whole group instructions:
The students will be given a copy of the reading materials the will be doing a silent reading for 10 minutes. The interactive discussion will follow.
- Reading analysis about basic information on WiFi Security
What is WiFi?
Wireless connectivity, often known as WiFi, is the technology that allows a PC, laptop, mobile phone, or tablet device to connect at high speed to the internet without the need for a physical wired connection. WiFi (pronounced “Why-Fy”) is a term that was coined by a branding company in 1999 as a name which would be easily recalled, due to its similarity to the then well-known term “hi-fi”.
The technology uses radio signals to transmit information between your WiFi enabled devices and the internet, allowing the device to receive information from the web in the same way that a radio or mobile phone receives sound.
Wireless security is the prevention of unauthorized access or damage to computers using wireless networks. The most common types of wireless security are Wired Equivalent Privacy (WEP) and WiFi Protected Access (WPA). WEP is a notoriously weak security standard.
https://www.consumer.ftc.gov/features/feature-0038-onguardonline
Which type of security is best for WiFi?
Setting up WEP, WPA or WPA2 wireless security
Security |
Rank |
| WEP Wired Equivalent Protocol | Basic |
| WPA Personal WiFi Protected Access® Personal | Strong |
| WPA2 Personal WiFi Protected Access® 2 Personal | Strongest |
| WPA2/WPA Mixed Mode | WPA2: Strongest WPA: Strong |
Resources:
https://3g.co.uk/guides/what-is-WiFi-explained-in-simple-terms
https://ieeexplore.ieee.org/iel7/7936435/7942803/07943094.pdf
- Answering the guided questions based on the reading materials presented to the students:
Discussion Question: How safe is public Wi Fi?
Go to the web to support your answer
https://lifehacker.com/top-10-ways-to-stay-safe-on-public-WiFi-networks-1791800347
Tiered Instruction
The students will be placed in groups based on their level.
Tier 1: Game The students will play the scavenger hunt game using the web provided
https://ieeexplore.ieee.org/iel7/7936435/7942803/07943094.pdf
Tier 2: Graphic Organizer
The students will read and create their own graphic organizer on the tips for Wi Fi security. Refer to the web:
14 Tips for Public WiFi Hotspot Security | PCMag.comhttps://www.pcmag.com/feature/254312/14-tips-for-public-WiFi-hotspot-security
Tier 3: Making a Diagram
The student will create their own design and draw the connection on how Wi Fi works on their paper with the sample provided by the teacher.
Device—-establish WiFi connection with a router—-connected to the Internet with DSL or cable modem.
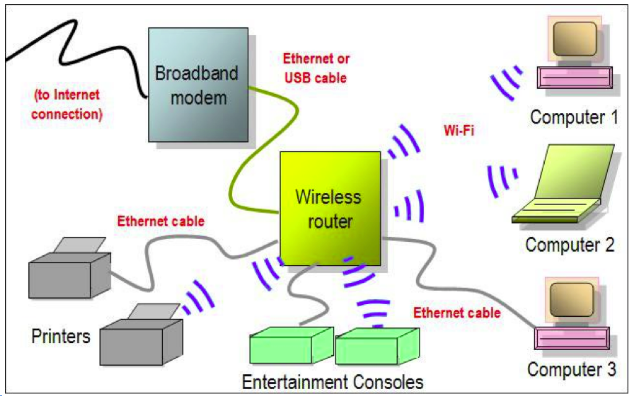
https://www.google.com/search?q=wi+fi+connection+diagram&client=ubuntu&hs=GuY&channel=fs&
Summary:
Wrap up the lesson by watching the video:
https://www.consumer.ftc.gov/features/feature-0038-onguardonline
Assessment:
- http://wififorbeginners.com/quizzes/module-1-quiz/
- The students will create a poster to inform the public on WiFi safety
Enrichment/Follow-up:
The students will research on the following questions:
- What are the benefits to “the cloud” and what are the risks?
- What is an easy rule to remember with USB devices? (If it’s not mine, don’t touch it-could be carrying malware/viruses).
- What might the storage of data look like in the future?
- Is there something better than the cloud?
- What do you prefer a USB, a school network storage drive, or the cloud? Why do you prefer the method? What are the positives and negatives of your choice? Have you ever experienced an issue or problems retrieving your stored information? How was it handled?
- If you do not have experience in data storage yet, What is the best practice to store data a USB or cloud storage?
Rubric for assessing the follow up enrichment questions. Please refer to:
iRubric: Answering Short Answer Questions rubric – U66W43: RCampus
https://www.rcampus.com/rubricshowc.cfm?code=U66W43&sp=true
© 2018 Teach Cyber
This work is licensed under a Creative Commons Attribution-Noncommercial-Share Alike 4.0 International License.
